Raise the cost of attacking your organization
Every week, established organizations are compromised. Not because they lack tools, but because they rely on outdated security architecture. It does not have to be that way.





Every week, established organizations are compromised. Not because they lack tools, but because they rely on outdated security architecture. It does not have to be that way.





We introduce the security innovations that the mainstream market overlooks



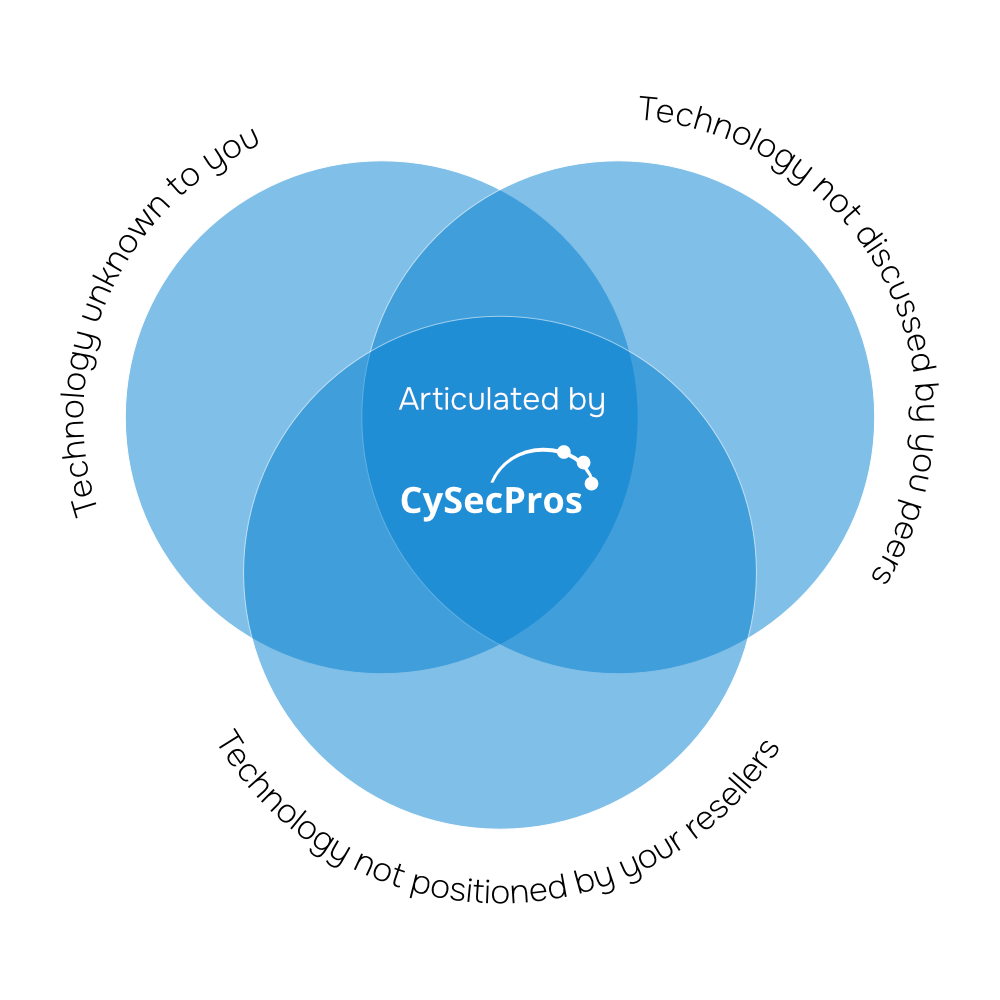

For many large organizations, the reality is that security architecture lags 3–5 years+ behind what is currently possible and sensible.


It is easier, and perceived as safer, for both legacy resellers and customers to stay with familiar solutions rather than challenge established models.

However, this approach materially weakens your security posture while increasing compliance, financial, and operational risk

Do we promise you will never be compromised? — No.
Do we help you significantly reduce the likelihood and impact?
– Absolutely.
While many organizations continue to layer new controls onto legacy architecture, our customers are fundamentally rethinking how security and governance are enforced across their most critical SaaS and web application environments.
Instead of accepting fragmented visibility, operational drag, and reactive compliance, they retire outdated control models and replace them with modern, integrated approaches that deliver deeper insight, stronger protection, faster performance, and a significantly simpler operating model.
The question is not whether your current stack works, but whether it is structurally built for today’s threat landscape.

If you are serious about reducing structural risk and modernizing your security architecture, let’s start the conversation.